Reveal
and Foresee
Threats
Reveal & Foresee Threats
At Aeteos™, our deep commitment to threat intelligence is driven by a core mission: to empower the heroes on the front lines, law enforcement agencies, military forces, forensic experts, and NGOs, with sovereign, ethical, and human-centered tools that transform sensitive textual data into clear, actionable intelligence.
Beyond high-stakes security, Percipion™ also enables organizations across all sectors to significantly improve decision-making and operational efficiency. It allows them to build their own sovereign cognitive platform and modernize a wide range of critical use cases.
Percipion™ delivers real-time, fully sovereign textual intelligence, helping security teams uncover hidden risks and anticipate emerging threats every day.
Whatever your field, Percipion™ accelerates information analysis, enhances decision-making, and complements your teams’ expertise. Operating on your own data and remaining completely under your control, it provides reliable insights even in areas where human expertise is limited, freeing your teams to focus on higher-value activities.
Years of R&D
Software Services
Knowledge Domains
Total resilience
Total resilience is the capacity of a system, organization, or society to prepare for shocks, resist their immediate impact, respond effectively to contain and mitigate damage, and recover swiftly while emerging stronger and better adapted.
It combines proactive anticipation, robust defense mechanisms, agile crisis management, and adaptive learning to maintain core functions and values under severe stress, whether from cyberattacks, disinformation, natural disasters, or geopolitical shocks, ensuring continuity and long-term viability.
Percipion™ acquire textual content, represent it within its internal memory, searches for related engrams across contextually connected knowledge schemas, and links those that are relevant to their parent symbolic object in order to understand, better evaluate threats and act with anticipation.
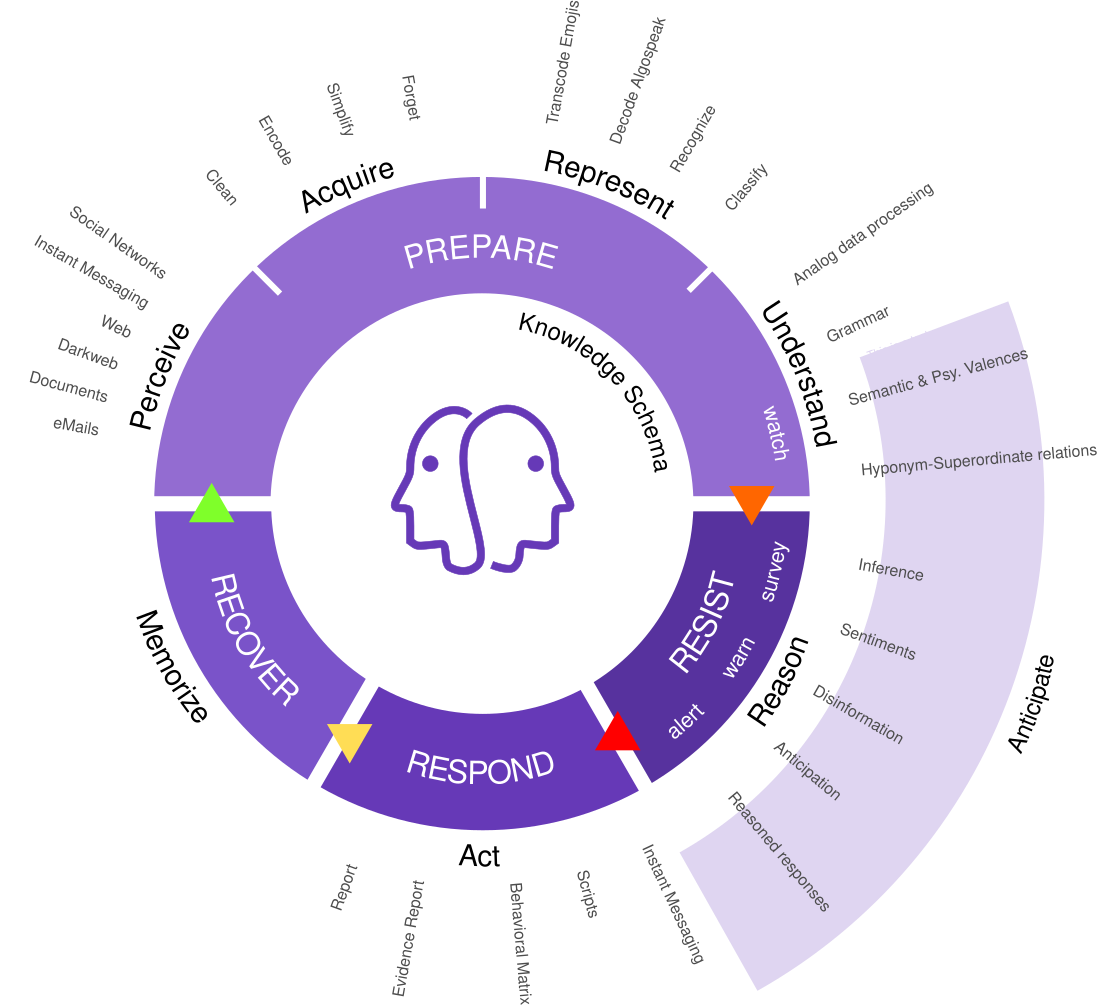
Prepare
Monitor continuously, identify patterns & flag actors
Resist
Evaluate threat level (survey, warn or alert)
Respond
Extract evidences to support & accelerate human intervention
Recover
Assess contextual semantic noise to uncover overlooked patterns and build long-term resilience (bias-free processing)
Beyond threat intelligence, Percipion™ supports ...
HR and talent teams by analyzing employee communications and feedback to detect low morale, uncover root causes of attrition, identify psychosocial risks, and evaluate motivation, job satisfaction, and transformation initiatives, helping organizations proactively safeguard workforce well-being and retention.
Marketing & sales, protecting brand reputation, uncovers purchase motivations and behavioral profiles, analyzes campaigns and competition in real time, and identifies ambassadors vs. critics, helping organizations prevent client loss, outmaneuver competitors, and drive more targeted, resilient growth.
Customer experience and support, analyzing interactions in real time to identify dissatisfied customers early, monitor complaints, evaluate overall satisfaction, optimize ticket routing, and decode tone/emotions, helping teams reduce churn, boost resolution speed, and deliver more empathetic, proactive service.
A short example : how Percipion supports forensics
Percipion can empower digital forensic analysts to assess in real time and in a fine manner information available in natural language on seized devices. It be daily used to find digital evidences, better understand criminal’s behaviour and contribute to the constitution of the digital identity of the person questioned.
Like Max who is in charge of hunting down pedocriminals. He arrested an individual suspected of child sexual abuse and remanded him in custody for 48 hours. Right now, he is racing against time. He gained a warrant on one chat group, and once the data are extracted and available, he will have to assess it quickly to find relevant illegal content. And today, Max has 373 pages of plain text to read. Just 30 hours are left to find evidences. To properly complete all this work, it would take him 5 days. If he would use Percipion, the same work would be done under 1 minute.
Messages to assess
pages of text
Done under one minute
It is as if this platform employs assistants capable of reading text, understanding, and grasping its nuances, identifying words and associating them with concepts, extracting meaning from text through precise contextual analysis, anticipating, reasoning, and drawing conclusions, producing reports, communicating, and taking action.
Your benefits
Powered by sovereign symbolic cognitive computing, Percipion™ excels at real-time processing of sensitive textual data, unlocking hidden inferences and strategic foresight.
In threat intelligence, forensics, and cognitive defense, it reveals concealed risks while anticipating emerging threats through weak-signal monitoring, accelerating decisions across high-stakes use cases.
Percipion™ delivers explainable expertise where human limits apply, enabling teams to focus on action and resilience while safeguarding sensitive information offline and ethically.
– 100% sovereign & developed in France by Aeteos™
– No foreign dependencies or third-party components
– No access, no reuse, no storage of your sensitive data
– Offline real-time processing, zero cloud exposure
– Hosted wherever you choose, on-prem or private cloud infrastructure
– Transparent & fully explainable execution, no black-box risks
– Knowledge based, bias-resistant, no discriminatory outcomes
– Eco-responsible with a low energy footprint
– Instant value, no learning phase, ready to deliver results from day one
– Superior detection of weak signals
– Advanced psychological & valency analysis
– Precise interpretation of emotions, intent, emojis & Algospeak
Percipion™, our secure Symbolic Cognitive Platform, has been designed using our latest innovations. These innovations are not used to promote our technological advances, but to improve the usability and analytical capabilities of our solutions to enhance professionals’ capabilities.
Data security
The security of our customers’ data is a priority.
To ensure its confidentiality and integrity, Percipion™ uses a proprietary encryption service to protect against cyberattacks. Once encrypted, whether at rest or in transit, your data can only be read and used by authorised parties.
Based on none of the known standardised algorithms, this solution provides a form of ‘obscurity’ that will make your data less attractive (HNDL attacks) and undermine cryptanalysis attempts, even post-quantum ones, particularly attacks based on predictable patterns. Therefore, you can dedicate a storage space on your platform for sensitive corporate data.
For customers who wish to do so, our ACrypt™ encryption solution is also available as a standalone software product.
Our knowledge schemas
Percipion™ uses a data structure similar to human long-term memory (the VirtualBrain™), where information is represented symbolically and categorised, enabling the machine to contextualize and process information. Its current version has 1,110 prototypical and abstract objects linked to 33,716 properties.
Psychology
Affective states, primary and secondary emotions, human needs, factors of job satisfaction and dissatisfaction, social skills (soft skills), factors contributing to work-related illnesses (boreout, brownout, burnout), customer experience analysis, and specific business context related knowledge schemas.
Protection
Corruption, conflicts of interest, misinformation, conspiracy theories, scams, coercive control tactics, psychological manipulation tactics (grooming), harassment, self-harm, sex trafficking and related practices, drug trafficking and related uses, trafficking in counterfeit goods and forgeries, trafficking in weapons and explosives, hate speech and hate crimes, ultra-violent content, pedocrimes, porncrimes and paraphilia, ableism, masculinism, and accelerationism.
Technical corner
Percipion™ enables companies to create their own microservices or cognitive computing solutions. It can smoothly be integrated into existing solutions or automated workflows.

At Aeteos™, we are committed to the quality of our software products. We have created all our libraries ourselves, without any dependence on other technologies. We have also produced dedicated applications to generate source code and check for programming errors. This constant pursuit of excellence and obsession with correcting even the smallest details make our software products safe and reliable.
Standalone
A proprietary software assistant that does not use any third-party components
Hosting
It can be installed on your workstation or infrastructure in minutes
Files
Can analyse large files (tested with 28 million characters)
Offline use
Highly secure, can be used without a network connection
Eco-friendly
Low footprint, energy consumption of 2.37Wh (2 400 times less energy than an LLM)
Trust
Knowledge-based, cannot be poisoned (secure)
Parallel execution
Can be executed in parallel on multiple cores for faster computation
Performance
Up to 61 files per second and 55 times faster than some of our competitors
Ready to build a safer Europe together?
We would love to hear from you. Whether you want to learn more about Percipion, request a demonstration, or explore how our human-centered cognitive solutions can support your organization, our team is here to help.
White paper
Please click on the button below to display and download a white paper about what we do
Question
Please click on the button below to send us your question via eMail
Demo
Please click on the button below to explain your needs and request a demonstration
We have chosen not to include an online form on this page in order to prioritise your security and privacy. Our top priority is to avoid any automatic collection and storage of sensitive personal information (such as your email address, name, or message) on our servers. This significantly reduces cybersecurity risks, such as data leaks or cyberattacks, and ensures our compliance with strict data protection standards (GDPR in Europe). Instead, we invite you to contact us directly by email. This simpler, more human approach allows us to handle your requests in a personalised manner, with a tailored response.
